Your Neighborhood Technology Success partner
Why Businesses Choose Big Water Tech
Comprehensive IT Solutions
Big Water Technologies offers tailored business IT support solutions covering managed services, phone systems, cybersecurity, cloud services, and more.
Security and Compliance Experts
You can rest assured knowing we're security and compliance experts with the ability to protect your network while ensuring your environment exceeds regulatory requirements.
Exceptional Customer Service
Our team has been in the industry since the 1970s - allowing us to offer you informed, strategic insight while maintaining a high level of customer service.
Commitment to Client Success
You're far too busy to worry about technology. That's why your success is our success. We make IT work for you - so you can drive growth.
Client Success Stories
We currently use Big Water for our managed phone service and they are great! We have had issue with managed phone service providers in the past but Jenn is super responsive when we have an issue or need a new line added or removed. I would not hesitate to recommend Big Water for managed phone services, low voltage or other technology needs!
COLLEEN BUDDE
Franchise Owner at Office Evolution Troy
Our Clients Say It Best
We’re proud to earn top marks from our clients through Crewhu’s customer feedback program. Every response helps us improve - and confirms that our team is making a real difference through responsive, friendly, and effective IT support. When our clients succeed, we succeed - and that’s what drives everything we do.
Is Your Technology Becoming Too Complex
For What It Needs To Be?
John Lowery
CEO, Big Water Tech
Big Water Tech is Here to Help Keep IT Simple with Bespoke IT Services.
At BigWater Technologies, safeguarding the integrity and security of your IT system is non-negotiable. We're dedicated to optimizing your technology to enhance efficiency and power.
Feel like you’ve been down this road before?
If you've felt burned by managed IT support providers in the past, rest assured, we prioritize fostering lasting client relationships over maximizing profits. Our focus is on maximizing the potential of your current IT infrastructure while keeping costs in check – possibly even reducing them.
Contact us at (248) 220-7714 to kick-start crucial IT discussions tailored to businesses like yours. Let's redefine your IT experience together.
Schedule an Appointment Today
As Your Technology Success Partner,
We're Here to Help You Drive Growth With:
Simplified IT Management
BIGview offers proactive corporate IT support and IT management services of technology assets on a subscription basis.
VoIP & Hybrid Phone Systems
Desktop & Mobile App, as well as Service Management with flexible VoIP service.
Vendor Neutral Management
We provide a thorough needs assessment, available provider review, order management, issue management, and regular bill reviews.
Comprehensive Equipment Support
We take care of your network security, switching, WiFi, servers, computers, video conferencing, and more.
Installation & Support
Low voltage cabling, paging, and camera systems designed to fit the needs of your team.
Ongoing Evaluation and Planning
Stay focused on the success of your company with regular proactive business reviews.
Protect Your Business from Cyber Threats
Proactive monitoring, threat detection, and compliance-focused security solutions that safeguard your systems, data, and operations around the clock.
Responsive User Assistance
Fast, reliable technical support that resolves user issues, reduces downtime, and keeps your team productive.
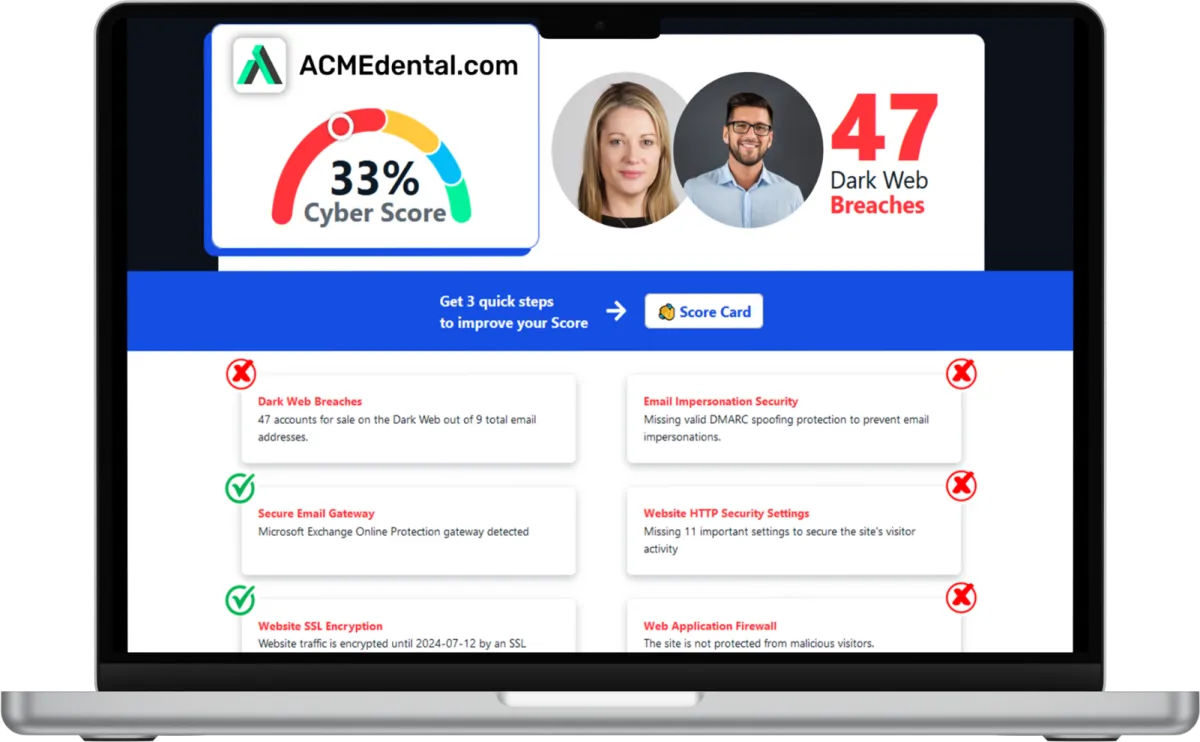
Want to see your Score? Get it in 30 seconds!
What Clients Say About Us
Delivering exceptional customer service is at the heart of our managed IT support services. Discover why businesses throughout Southfield and Metro Detroit rely on Big Water Tech for dependable IT and computer support.
Managing Your Security Has Never Been Simpler

Discover Your Cyber Score
Start by assessing your Cyber Score to understand your business’s online security. This score provides clarity, replacing uncertainty with insight, so you know exactly where you stand and what needs improvement.

Create Your Cyber Roadmap
Use your Cyber Score to develop a clear, actionable Cyber Roadmap. This plan highlights vulnerabilities and provides precise steps to strengthen your security, saving you time and resources. Schedule a meeting with Big Water Tech so we can help you create a clear, strategic path to cyber resilience.

Enhance Your Security
Put your Roadmap into action with a step-by-step approach to stronger protection. Demonstrate your commitment to safeguarding customer data while equipping your IT team with a focused, cost-effective security strategy.

Want to see your Cybersecurity Score? Get it in 30 seconds!
The More You Know...
Our blog shares practical guidance, expert takes, and real-world lessons drawn from the front lines of IT services & solutions. Stay informed, stay protected, and make smarter decisions for your business or organization.

The Access Nobody Reviews (Until Something Goes Wrong)
Most Michigan business owners believe cybersecurity failures start with hackers.
In practice, many breaches, audit issues, and insurance problems start with something far more ordinary.
Access that was never reviewed.
Not because anyone was careless.
Not because IT dropped the ball.
But because access quietly accumulates as firms grow, roles change, and people move on.
For professional service firms that handle sensitive client data, this is one of the most overlooked risks hiding in plain sight.
What Is “Unreviewed Access”?
Unreviewed access is when employees, contractors, or vendors retain permissions to systems or data they no longer need.
This commonly includes:
Employees who changed roles but kept old permissions
Former employees whose accounts were never fully removed
Temporary access granted “just in case” that became permanent
Shared logins used for convenience
Third-party tools or integrations that were never revisited
Access almost always expands over time.
Very few firms actively reduce it.
That gap between who should have access and who actually does is where risk lives.
Why Unreviewed Access Is a Business Risk
Access management is often treated as a technical detail.
It is not.
Unreviewed access directly affects:
Client confidentiality
Regulatory and compliance exposure
Cyber insurance eligibility and claims
Audit outcomes
Your firm’s reputation
When something goes wrong, the question is rarely:
“Did you intend for this person to have access?”
The question is:
“Why was the access still in place?”
Intent does not protect you during an audit, an insurance review, or a client dispute. Proof does.
Why This Risk Shows Up During Audits and Insurance Renewals
Auditors and cyber insurance carriers increasingly focus on who can access what inside your firm.
Common questions include:
Who has access to sensitive client or patient data?
How often is access reviewed?
What happens when someone changes roles or leaves?
Can you demonstrate least-privilege access?
Many firms answer confidently until they are asked to show documentation.
This is where well-run businesses get caught off guard. Not because they are unsafe, but because access decisions were never formally reviewed or recorded.
The Hidden Cost of “Everyone Needs Access”
Broad access feels efficient.
It avoids friction.
It keeps people productive.
It reduces complaints.
But it also:
Increases the impact of simple mistakes
Expands the scope of breaches
Makes investigations harder
Weakens your position with insurers and clients
Excess access does not improve productivity.
It increases the cost of problems when they occur.
Why Good Firms Miss This
Unreviewed access persists because it lives in the cracks.
It is not clearly owned by:
Leadership
HR
IT support
So it becomes everyone’s responsibility and no one’s job.
Most firms review passwords occasionally.
Very few conduct regular, documented access reviews tied to current roles and risk.
What “Good” Looks Like for SMBs
You do not need enterprise-level complexity.
A Smarter Business approach includes:
Clearly defined roles
Access aligned to current responsibilities
Scheduled access reviews
Documented decisions
The goal is not less access.
The goal is intentional access you can explain and defend.
A Question Every Business Owner Should Ask
If an auditor, insurer, or major client asked today:
“Who has access to your most sensitive systems and why?”
Could you answer clearly and confidently?
If the answer is “probably” or “I think so,” the risk already exists.
Not as a crisis.
As a gap.
Why This Risk Is Growing in 2026
Modern firms grant access faster than ever:
Cloud platforms
AI tools
Remote work
Vendor integrations
As systems multiply, access multiplies with them.
Firms that treat access as an ongoing business decision will reduce surprises. Firms that don’t will discover this risk at the worst possible moment.
Smarter Business Takeaway
Cybersecurity is not just about keeping the wrong people out.
It is about ensuring:
The right people have the right access
For the right reasons
At the right time
With proof to support it
That is how you protect client trust, insurance coverage, and long-term business value.
That is Smarter Business IT.
Frequently Asked Questions About User Access Risk
What is unreviewed user access?
Unreviewed user access refers to system permissions that remain active without regular review or justification, often after role changes, temporary projects, or employee departures.
Why is user access a cybersecurity risk?
Because unnecessary access increases the likelihood and impact of mistakes, breaches, and unauthorized data exposure.
How does access control affect cyber insurance?
Insurers increasingly require proof that access is reviewed and limited. Poor access controls can lead to higher premiums, exclusions, or denied claims.
What is least privilege for small businesses?
Least privilege means employees only have access to the systems and data they need to perform their current job responsibilities.
How often should access be reviewed?
Access should be reviewed when someone joins, changes roles, or leaves, and on a regular cadence such as quarterly or semi-annually.
Why do audits fail due to access issues?
Audits fail when firms cannot demonstrate who has access, why they have it, and how access decisions are reviewed and documented.
Want to know where your access risk stands today?
A structured access review will show you exactly who has access, where it makes sense, and where it doesn’t.
#SmarterBusiness #BigWaterTech #KeepITSimple
Our Services
Simple IT Management & Support
BIGview offers proactive management of technology assets on a subscription basis. BIGview is a service based offering designed specifically for your organization's requirements.
Hosted Voice
Desktop & Mobile App, SIP Firewall, and Service Management with flexible VoIP service. Powerful call control on a local business number you can access from anywhere.
Disaster Recovery & Backup
An automated data backup and restore system providing powerful tools to protect your organization's data. It doesn’t require any human assistance beyond the initial installation.
Managed Cloud Environment
Protecting your data is incredibly important. Our BIGcloud Server is highly secure, extremely reliable, easy to scale, and has simple and affordable pricing.
Managed File Sharing
BIGshare Managed Cloud Sharing is a secure, HIPAA & PCI compliant solution. Our BIGshare comes standard with backup and DRaaS all with unlimited storage for one simple price.
Managed Security
BIGprotect is a comprehensive fully-managed security solution. It provides a powerful way to protect your organization’s network .
Voice & Data Protection
BIGguard is a protection plan for your voice and data communications equipment. It provides a powerful way to protect your organization’s voice and data investment.
Security Assessment & Reporting
Elevate your security posture with our assessment and reporting solutions. Gain comprehensive insights into your organization's security landscape.
Take IT Off Your Plate...
Spend less time on IT problems and more time growing your business. Let’s get to know each other and determine how our partnership could grow. With us as your trusted MSP on your side, you can develop a strong barrier against cybercrime, stronger communication strategies, and a better technology plan for the future.
Call (248) 220-7714 today or fill out the form below to schedule your appointment. We’re ready to jumpstart your IT journey.