Your Neighborhood Technology Success partner
Why Detroit Businesses Choose Big Water Technologies
Comprehensive IT Solutions
Big Water Technologies offers tailored business IT support solutions covering managed services, business phone systems, cybersecurity, cloud services, and more.
Security and Compliance Experts
You can rest assured knowing we're security and IT compliance experts with the ability to protect your network while ensuring your environment exceeds regulatory requirements.
Exceptional Customer Service
Our team has been in the industry since the 1970s - allowing us to offer you informed, strategic insight while maintaining a high level of customer service.
Commitment to Client Success
You're far too busy to worry about technology and tech problems. That's why your success is our success. We make IT work for you - so you can drive growth, productivity, and have peace of mind.
Client Success Stories
We currently use Big Water for our managed phone service and they are great! We have had issue with managed phone service providers in the past but Jenn is super responsive when we have an issue or need a new line added or removed. I would not hesitate to recommend Big Water for managed phone services, low voltage or other technology needs!
COLLEEN BUDDE
Franchise Owner at Office Evolution Troy
Our Clients Say It Best
We’re proud to earn top marks from our clients through Crewhu’s customer feedback program. Every response helps us improve - and confirms that our team is making a real difference through responsive, friendly, and effective IT support. When our clients succeed, we succeed - and that’s what drives everything we do.
Is Your Technology Getting in the Way of Running Your Business?
You’re not alone, and it doesn’t have to be this complicated.
John Lowery
CEO, Big Water Tech
Big Water Tech is Here to Help Keep IT Simple with Our Reliable IT Support.
At BigWater Technologies, safeguarding the integrity and security of your IT system is non-negotiable. We're dedicated to optimizing your technology to enhance efficiency and power.
Feel like you’ve been down this road before?
If you've felt burned by managed services providers in the past, rest assured, we prioritize fostering lasting client relationships over maximizing profits. Our focus is on maximizing the potential of your current IT infrastructure while keeping costs in check – possibly even reducing them.
Contact us at (248) 220-7714 to kick-start crucial IT discussions tailored to businesses like yours. Let's redefine your IT experience together.
Schedule an Appointment Today
As Your Technology Success Partner,
We're Here to Help You Drive Growth With:
Simplified IT Management
BIGview offers proactive corporate IT support and IT management services of technology assets on a subscription basis.
VoIP & Hybrid Phone Systems
Desktop & Mobile App, as well as Service Management with flexible VoIP service.
Vendor Neutral Management
We provide a thorough needs assessment, available provider review, order management, issue management, and regular bill reviews.
Comprehensive Equipment Support
We take care of your network security, switching, WiFi, servers, computers, video conferencing, and more.
Installation & Support
Low voltage cabling, paging, and camera systems designed to fit the needs of your team.
Ongoing Evaluation and Planning
Stay focused on the success of your company with regular proactive business reviews.
Protect Your Business from Cyber Threats
Proactive monitoring, threat detection, and compliance-focused security solutions that safeguard your systems, data, and operations around the clock.
Responsive User Assistance
Fast, reliable technical support that resolves user issues, reduces downtime, and keeps your team productive.
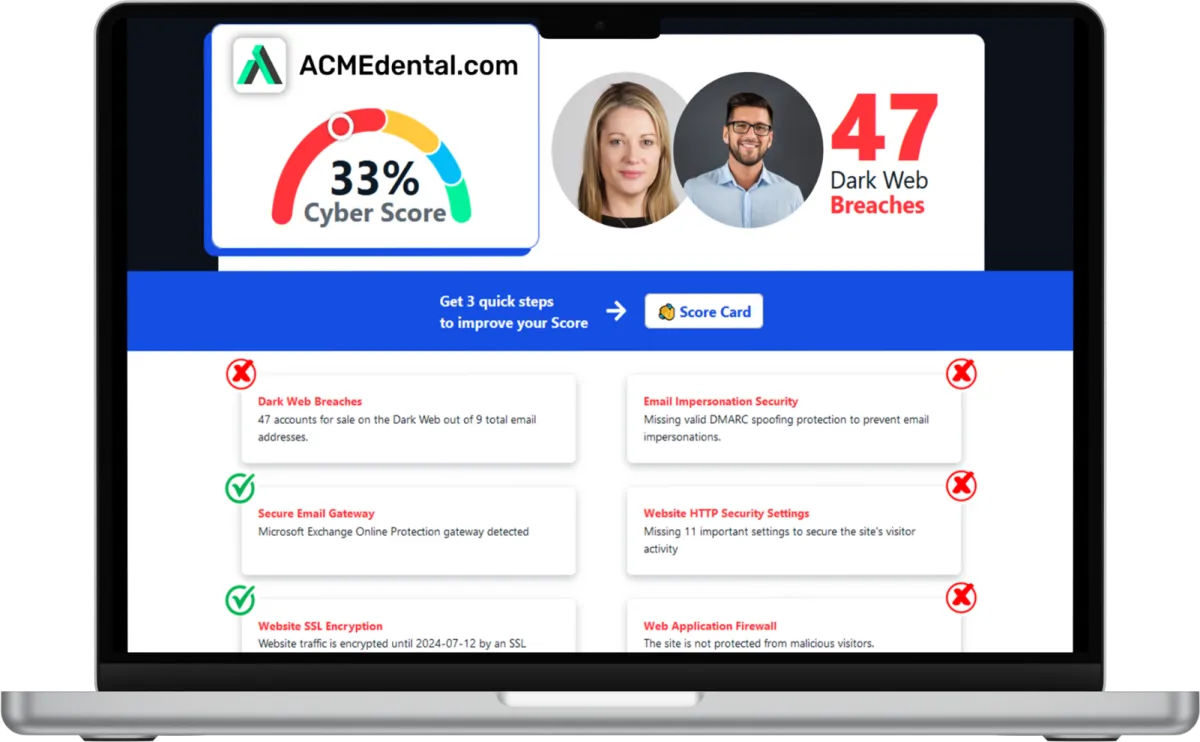
Want to see your Score? Get it in 30 seconds!
What Clients Say About Us
Delivering exceptional customer service is at the heart of our IT management support services. Discover why businesses in Detroit rely on Big Water Tech for dependable IT and computer support.
Managing Your Security Has Never Been Simpler

Discover Your Cyber Score
Start by assessing your Cyber Score to understand your business’s online security. This score provides clarity, replacing uncertainty with insight, so you know exactly where you stand and what needs improvement.

Create Your Cyber Roadmap
Use your Cyber Score to develop a clear, actionable Cyber Roadmap. This plan highlights vulnerabilities and provides precise steps to strengthen your security, saving you time and resources. Schedule a meeting with Big Water Tech so we can help you create a clear, strategic path to cyber resilience.

Enhance Your Security
Put your Roadmap into action with a step-by-step approach to stronger protection. Demonstrate your commitment to safeguarding customer data while equipping your IT team with a focused, cost-effective security strategy.

Want to see your Cybersecurity Score? Get it in 30 seconds!
Stay Ahead with Big Water Tech Insights
IT Wisdom Worth Reading for Growing Businesses
Our blog shares practical guidance, expert takes, and real-world lessons drawn from the front lines of IT services & solutions. Stay informed, stay protected, and make smarter decisions for your business or organization.

Why Cyber Insurance Isn't a Security Strategy
What small businesses need to know about cyber liability coverage, claim denials, and the gap between having a policy and being protected
What is cyber insurance, and what does it actually cover?
Cyber insurance (also called cyber liability insurance) is a policy designed to help businesses recover financially after a cyber incident, things like data breaches, ransomware attacks, business interruption, and legal liability.
But here's what many business owners don't realize: cyber insurance doesn't prevent attacks, and it doesn't guarantee payouts.
Most policies come with requirements. If you can't prove you met those requirements when you filed your application, your claim can be denied even if you've been paying premiums for years.
Why do businesses think cyber insurance is enough?
Cyber insurance has become a checkbox for many small and mid-sized businesses. They buy the policy, file it away, and assume they're covered if something happens.
The problem: the policy becomes an excuse not to invest in actual security controls.
Common assumptions that get firms in trouble:
"We have insurance, so we're covered if we get hit with ransomware."
"The policy will pay for everything, data recovery, legal fees, business interruption."
"We answered yes on the application, so we must have the controls in place."
These assumptions often don't survive contact with a real claim.
What are the most common cyber insurance requirements?
Most cyber insurance policies require businesses to have specific security controls in place. Common requirements include:
Multi-factor authentication (MFA) on all user accounts and remote access
Regular, tested backups with documented recovery procedures
Endpoint detection and response (EDR) on all devices
A written incident response plan
Security awareness training for employees
Access logging and monitoring
If you attested to having these controls on your application but can't prove they're actually in place, you're at risk of a denied claim.
Can a cyber insurance claim be denied? What causes claim denials?
Yes. Cyber insurance claims are denied more often than most business owners realize.
The most common reason for denial: material misrepresentation.
This means you said something on your application that wasn't accurate, either intentionally or because you didn't verify before answering.
Examples that lead to denied claims:
Attesting to MFA on all accounts when it was only enabled on some
Claiming backups are tested regularly when they haven't been verified in months
Saying you have an incident response plan when it's never been documented or practiced
Answering "yes" to security controls that exist on paper but aren't enforced
Carriers aren't just asking questions anymore, they're verifying answers. If your attestation doesn't match reality, your claim is at risk.
What does "material misrepresentation" mean in cyber insurance?
Material misrepresentation is when a business provides inaccurate information on an insurance application that affects the insurer's decision to provide coverage or set premiums.
In cyber insurance, this often happens when:
The person filling out the application doesn't actually know the current state of security controls
The IT person says "yes" to questions because that's what they've always said
Nobody verifies whether attested controls are actually in place and working
The result: When a claim is filed, the carrier investigates. If they find gaps between what was attested and what's actually in place, they can deny the claim based on material misrepresentation.
The policy exists. You paid the premium. But it won't pay out.
What's the difference between having cyber insurance and being protected?
Having cyber insurance means you have a financial backstop if something goes wrong.
Being protected means you have the controls, processes, and documentation in place to:
Reduce the likelihood of an incident
Respond effectively if one occurs
Prove to your carrier that you met your policy requirements
Cyber insurance is part of a security strategy. It's not the strategy itself.
Firms that treat insurance as a substitute for security often find out too late that the policy won't cover them when they need it most.
How can businesses make sure their cyber insurance will actually pay out?
Here's how to close the gap between having a policy and being protected:
1. Read your policy. Actually read it
Know what's covered, what's excluded, and what requirements you agreed to meet. If you can't explain your coverage in plain English, you don't understand it well enough.
2. Review your application
Pull out the application you signed. Look at every question you answered "yes" to. Can you prove each one with documentation? If the answer is "I'd have to check with IT," that's a red flag.
3. Verify your controls
Don't assume controls are in place because someone said they were. Test your backups. Confirm MFA is enabled everywhere. Review your incident response plan. Document everything.
4. Close gaps before renewal
If there's a gap between what you attested to and what's actually in place, fix it now not after an incident, not at renewal time.
5. Separate attestation from implementation
The person filling out the questionnaire shouldn't be the same person who set up the controls. Get outside verification of your security posture before you sign.
What should small businesses do before their next cyber insurance renewal?
Before your next renewal, ask yourself:
When was the last time we actually read our policy?
Can we document every control we attested to on the application?
Have we tested our backups in the last 90 days?
Is MFA enabled on all accounts, not just some?
Do we have a written incident response plan that's been reviewed this year?
Who's verifying that our controls actually work?
If you can't answer these questions confidently, you have work to do before renewal.
The Bottom Line
Cyber insurance is a financial tool, not a security strategy.
The businesses that get value from their policies are the ones who did the security work first. They can answer the carrier's questions without scrambling. They can prove what they attested to. They treated insurance as a backstop, not a checkbox.
Keep IT Simple. Insure what you've secured.
If you're not sure whether your security controls match what's on your cyber insurance application, it's worth finding out before your carrier does. Contact Big Water Technologies to discuss a security assessment for your Michigan firm.
Our Services
Simple IT Management & Support
BIGview offers proactive management of technology assets on a subscription basis. BIGview is a service based offering designed specifically for your organization's requirements.
Hosted Voice
Desktop & Mobile App, SIP Firewall, and Service Management with flexible VoIP service. Powerful call control on a local business number you can access from anywhere.
Disaster Recovery & Backup
An automated data backup and restore system providing powerful tools to protect your organization's data. It doesn’t require any human assistance beyond the initial installation.
Managed Cloud Environment
Protecting your data is incredibly important. Our BIGcloud Server is highly secure, extremely reliable, easy to scale, and has simple and affordable pricing.
Managed File Sharing
BIGshare Managed Cloud Sharing is a secure, HIPAA & PCI compliant solution. Our BIGshare comes standard with backup and DRaaS all with unlimited storage for one simple price.
Managed Security
BIGprotect is a comprehensive fully-managed security solution. It provides a powerful way to protect your organization’s network .
Voice & Data Protection
BIGguard is a protection plan for your voice and data communications equipment. It provides a powerful way to protect your organization’s voice and data investment.
Security Assessment & Reporting
Elevate your security posture with our assessment and reporting solutions. Gain comprehensive insights into your organization's security landscape.
Frequently Asked Questions
What does an MSP (Managed Services Provider) do?
An MSP proactively monitors, maintains, and secures your IT environment so your business runs smoothly. Big Water Tech handles backups, patching, help desk support, and cloud services, giving you predictable costs, faster response times, and a reliable technology success partner focused on your success across Detroit.
Why choose a local MSP in Southfield and Detroit?
Choosing a local MSP means faster on‑site support, better understanding of regional business needs, and more personalized service. Big Water Technologies is a Southfield‑based Technology Success Partner that serves Detroit, offering managed IT services, cloud solutions, VoIP, and IT consulting that align with your local operations and growth goals.
How does Big Water Technologies’ BIGVoice VoIP phone system work?
Big Water Technologies’ BIGVoice business VoIP phone system uses the internet to deliver voice calls, conferencing, and advanced features across your office and remote teams. It integrates with your existing IT environment, scales with your business, and reduces phone‑line costs while improving reliability and communication tools for your Metro Detroit‑area organization.
How does Big Water Tech approach cybersecurity?
Big Water Tech takes a proactive, layered approach to cybersecurity, combining threat monitoring, endpoint protection, secure backups, and employee training. We assess your unique risks, implement tailored defenses, and continuously update your security posture to protect data, systems, and compliance across your Detroit organization.
What are the benefits of outsourcing IT support and services?
Outsourcing IT support gives you access to expert resources without the overhead of an in‑house team. With Big Water Tech, you gain faster response times, reliable help desk support, scalable cloud solutions, and stronger cybersecurity, so your Detroit business stays agile, secure, and focused on growth.
Take IT Off Your Plate...
Spend less time on IT problems and more time growing your business. Let’s get to know each other and determine how our partnership could grow. With us as your trusted MSP on your side, you can develop a strong barrier against cybercrime, stronger communication strategies, and a better technology plan for the future.
Call (248) 220-7714 today or fill out the form below to schedule your appointment. We’re ready to jumpstart your IT journey.